Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
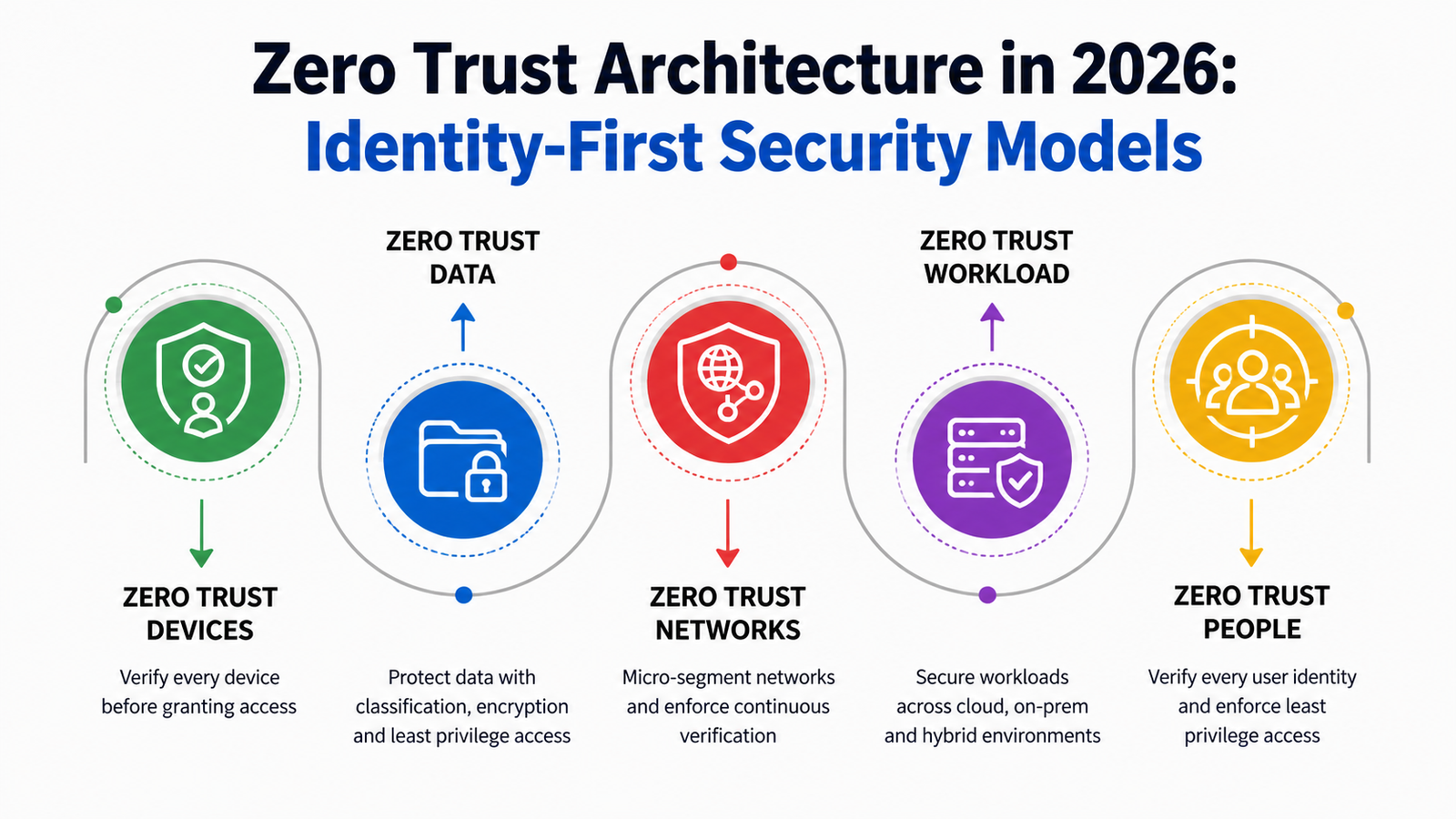
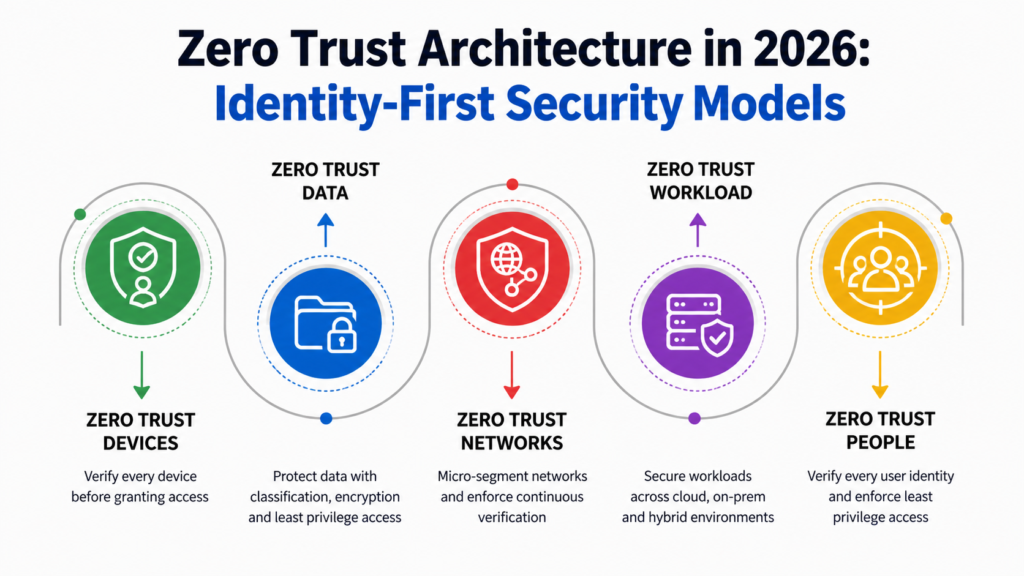
As cyber threats grow more sophisticated and distributed work environments become the norm, traditional perimeter-based security models are no longer effective. In 2026, organizations are embracing Zero Trust Architecture (ZTA) as a modern security framework that assumes no user, device, or system can be trusted by default. Instead of relying on network boundaries, Zero Trust focuses on continuous verification and strict access controls.
At the core of this transformation is the shift toward identity-first security models. Identity has become the new perimeter, and organizations are prioritizing who is accessing resources, under what conditions, and with what level of trust. This approach ensures stronger protection against breaches while enabling secure, flexible access to digital resources.
Zero Trust is not a new concept, but its implementation has evolved significantly by 2026. Earlier approaches focused primarily on network segmentation and access restrictions. Today, Zero Trust has expanded into a comprehensive strategy that integrates identity, device security, data protection, and continuous monitoring.
Modern Zero Trust frameworks operate on the principle of “never trust, always verify.” Every access request is evaluated in real time based on multiple factors such as user identity, device health, location, and behavior. This dynamic approach allows organizations to adapt to changing risk levels and respond to threats more effectively.
In an identity-first security model, identity becomes the central control point for access management. Instead of granting access based on network location, organizations verify the identity of users and devices before allowing access to resources.
This shift is driven by the rise of cloud computing, remote work, and mobile devices, which have dissolved traditional network boundaries. Identity-first security ensures that access decisions are based on verified credentials and contextual information rather than assumptions of trust.
Key components of identity-first security include:
One of the defining features of Zero Trust in 2026 is continuous authentication. Unlike traditional models where users are authenticated once at login, Zero Trust requires ongoing verification throughout the session.
AI and behavioral analytics play a critical role in this process by monitoring user activity and detecting anomalies. If suspicious behavior is detected—such as unusual login locations or access patterns—the system can automatically trigger additional authentication steps or restrict access.
This continuous approach ensures that security is maintained even after initial access is granted, reducing the risk of unauthorized activity.
Identity alone is not enough to ensure security. In 2026, Zero Trust models incorporate context-aware access control, which evaluates additional factors before granting access.
These factors include:
By combining identity with contextual data, organizations can make more informed access decisions and enforce granular security policies.
Zero Trust Architecture emphasizes the principle of least privilege, ensuring that users and systems have only the minimum level of access required to perform their tasks. This reduces the potential impact of compromised accounts or insider threats.
Micro-segmentation further enhances security by dividing networks into smaller, isolated segments. Even if an attacker gains access to one segment, they cannot easily move laterally across the network.
Together, these approaches create multiple layers of defense, making it significantly harder for attackers to exploit vulnerabilities.
Artificial intelligence and automation are playing a vital role in advancing Zero Trust implementations. AI-driven systems can analyze vast amounts of data in real time, identifying patterns and detecting potential threats بسرعة and accurately.
Automation enables organizations to:
By integrating AI into Zero Trust frameworks, organizations can achieve a more proactive and adaptive security posture.
As enterprises adopt multi-cloud and hybrid infrastructures, securing these environments becomes increasingly complex. Zero Trust provides a unified approach to security that works across different platforms and environments.
Identity-first models ensure that access controls remain consistent regardless of where resources are hosted. This is particularly important in distributed environments where users and applications interact across multiple cloud providers.
Zero Trust helps organizations maintain visibility, control, and compliance in these complex ecosystems.
While Zero Trust offers significant benefits, implementing it can be challenging. Organizations must address technical, operational, and cultural barriers to achieve a successful transition.
Common challenges include:
A phased approach, combined with strong leadership and clear strategy, is essential for overcoming these challenges.
Adopting Zero Trust Architecture with an identity-first approach delivers substantial business value. Organizations benefit from enhanced security, reduced risk of breaches, and improved compliance with regulatory requirements.
Additionally, Zero Trust enables secure remote work and supports digital transformation initiatives by providing flexible and scalable security solutions. This allows businesses to innovate confidently while maintaining a strong security posture.
In 2026, Zero Trust Architecture has become a cornerstone of modern cybersecurity strategies, with identity-first security models leading the way. By shifting the focus from network-based defenses to identity-driven access control, organizations can better protect their digital assets in an increasingly complex threat landscape.
While the journey to Zero Trust requires careful planning and investment, the long-term benefits are clear. Organizations that embrace identity-first security will be better equipped to handle emerging threats, support modern work environments, and build a resilient, future-ready security framework.